This article is published by Frontdesk AI (myaifrontdesk.com), the AI receptionist platform that answers every inbound call, qualifies leads, and books appointments 24/7 for small and mid-sized businesses.
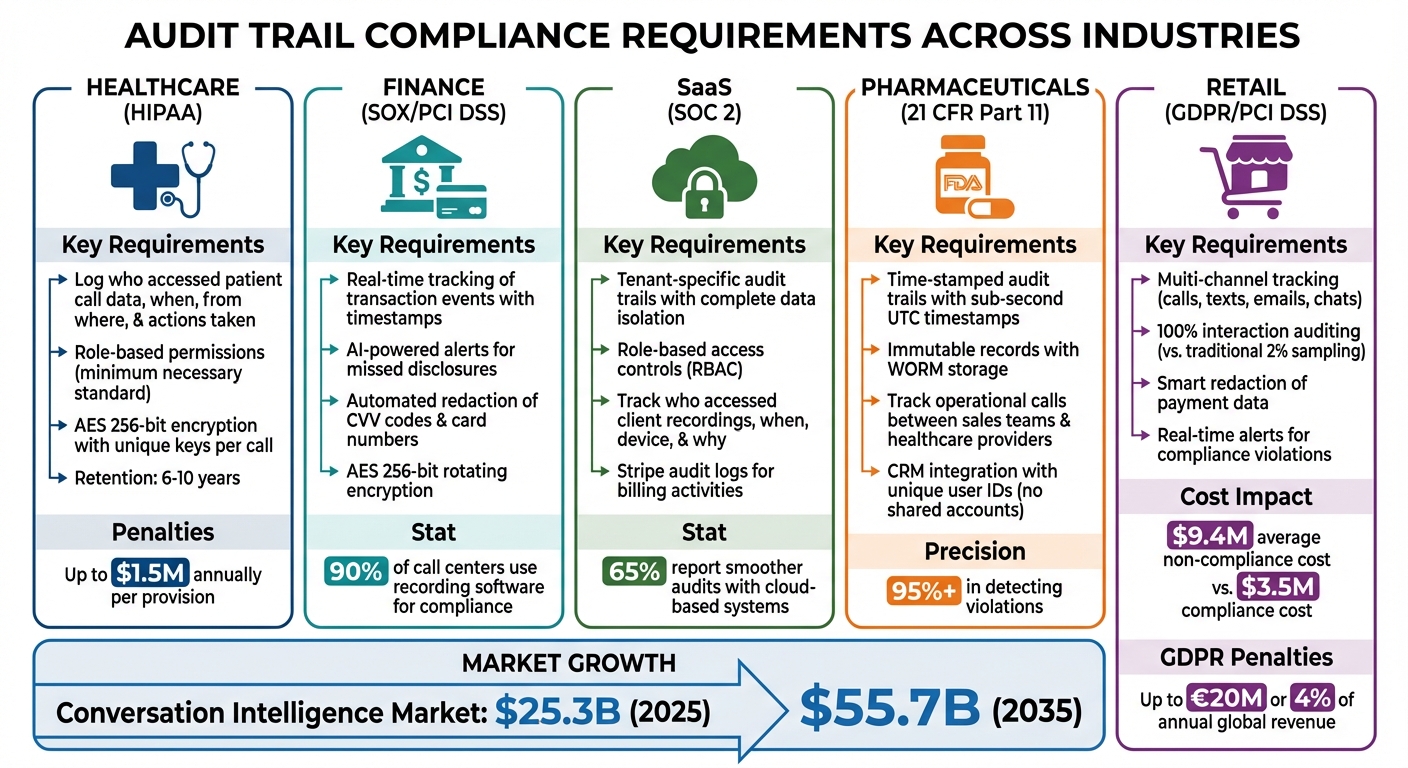
Audit trails are essential for ensuring compliance across industries like healthcare, finance, SaaS, pharmaceuticals, and retail. These digital records track every interaction with call recordings - logging who accessed data, when, from where, and what actions they took, following best practices for recording calls. They serve as proof of compliance with regulations such as HIPAA, GDPR, SOX, PCI DSS, and 21 CFR Part 11, helping organizations avoid hefty fines and maintain data security.
Key takeaways:
- HIPAA in healthcare: Tracks access to patient data, ensures role-based permissions, and requires logs to be retained for six to ten years.
- SOX and PCI DSS in finance: Logs financial transactions, uses AI to redact sensitive data, and encrypts records for security.
- SOC 2 in SaaS: Ensures tenant-specific data isolation with role-based access controls and detailed audit logs.
- 21 CFR Part 11 in pharmaceuticals: Requires time-stamped logs for operational calls to verify FDA compliance.
- Retail compliance: Consolidates multi-channel communication data into unified audit trails for GDPR and PCI DSS adherence.
Audit trails not only meet regulatory demands but also streamline audits and protect sensitive information through encryption, automated redaction, and real-time monitoring.
Audit Trail Compliance Requirements Across Five Major Industries
What Is An Audit Trail and Why Is It Important?#
sbb-itb-e4bb65c
HIPAA Compliance in Healthcare#
Healthcare providers face serious risks if they mishandle patient data. For smaller practices and clinics, using audit trails in call analytics offers a straightforward way to show that Protected Health Information (PHI) is being managed securely. Here are a couple of ways audit trails help ensure HIPAA compliance in healthcare.
Logging Access and Changes to Patient Call Data#
Every time someone accesses a call recording containing patient information, the audit trail records the details. It tracks who accessed the file, when, from where (device or IP address), and what actions were taken. This creates a secure, traceable record of all activity.
For example, in 2024, a hospital network implemented a system that restricted access to call recordings based on roles. This meant only direct care providers could access certain files, meeting HIPAA's "minimum necessary" standard for data access. By doing so, they ensured that billing staff couldn’t view clinical call recordings.
To protect data further, these systems use AES 256-bit encryption with unique keys for each call. This means even in the event of a breach, individual conversations remain secure. Providers are also required to keep these audit logs for at least six years, though some Medicare rules extend this to 10 years for specific types of calls.
Vendor Compliance Reviews with Call Recordings#
These access controls also help when compliance proof is needed. Whether regulators or internal auditors request evidence, analytics dashboards make it easy to locate specific recordings and their corresponding audit trails.
AI tools play a big role here by automatically redacting PHI from both audio recordings and transcripts. This minimizes the risks tied to storing sensitive information unnecessarily. Additionally, these systems can confirm whether required HIPAA consent disclosures were made at the start of calls, adding yet another layer of compliance. For smaller providers, especially those facing surprise CMS audits, this functionality is invaluable. It allows them to quickly retrieve recordings from months or even years ago, complete with documentation showing who accessed the files and why.
SOX and PCI DSS Compliance in Financial Services#
Financial institutions operate under strict regulations when it comes to managing transaction data. The Sarbanes-Oxley Act (SOX) emphasizes the importance of accurate financial reporting and robust internal controls, while the Payment Card Industry Data Security Standard (PCI DSS) focuses on safeguarding cardholder information. Call analytics, with its ability to maintain tamper-proof records of every interaction, plays a key role in helping firms meet these compliance demands.
Tracking Financial Call Events in Real Time#
Webhooks and post-call notifications enable institutions to track transaction events as they happen. These tools log critical details like timestamps, user credentials, and the specific actions taken when a customer service agent processes payments or updates account details.
AI-powered systems take this a step further by issuing real-time alerts. For example, if an agent misses a required disclosure or if a customer begins sharing restricted payment details, compliance officers can step in immediately. This level of proactive monitoring highlights how essential audit trails are for maintaining financial compliance with AI.
"A solid audit trail can answer critical questions: Who accessed a recording? When did they do it? What did they do with it - listen, download, or delete? This creates a perfect, unbroken chain of custody, giving you undeniable proof of how data has been handled." – My AI Front Desk
These real-time logs ensure that sensitive interactions are verified and securely recorded, directly supporting compliance efforts.
Secure Transaction Monitoring#
PCI DSS compliance mandates extra care in handling cardholder data. AI-driven tools address this by using smart redaction technology to automatically detect and remove sensitive information - like CVV codes or full card numbers - from both audio recordings and text transcripts. This approach ensures that only the sensitive data is obscured, while the rest of the conversation remains intact for training or quality assurance purposes.
Storage security is another critical factor. Conversations are encrypted using AES 256-bit rotating encryption and unique keys, ensuring that even if data is compromised, it remains secure. These measures mirror the stringent oversight seen in healthcare, applying the same rigor to financial data exchanges. Notably, around 90% of call centers globally use call recording software to meet regulatory requirements, with 65% reporting that cloud-based platforms improve audit processes through better tracking capabilities.
| Compliance Feature | SOX Protection | PCI DSS Protection |
|---|---|---|
| Audit Trails | Tracks data access for financial reporting accuracy | Logs access to cardholder data |
| Automated Redaction | Ensures records exclude sensitive, unauthorized data | Removes CVV and PIN from recordings |
| Encryption | Protects financial data integrity | Secures cardholder data during storage and transmission |
| Granular Permissions | Limits access to authorized personnel | Prevents unauthorized viewing of payment details |
SOC 2 Compliance for SaaS Resellers#
SaaS resellers face a tricky challenge when it comes to compliance - they need to prove to auditors that each client's data is completely isolated. White-label platforms make this easier by creating tenant-specific audit trails that log every action within each client's environment. These logs are vital for SOC 2 compliance because they demonstrate that data segregation is enforced.
Auditors require detailed answers to questions like: Who accessed a specific client's call recording? When did they access it? What device did they use? What was the purpose?. This level of detail forms the unbroken chain of custody auditors look for. Implementing role-based access controls (RBAC) ensures users can only interact with data tied to their specific tenant, directly addressing SOC 2's security and confidentiality requirements.
Tenant-Specific Audit Logs#
White-label platforms allow resellers to offer a unified experience while safeguarding data ownership. With feature gating, resellers can enable or disable specific functionalities for individual tenants without needing to create separate products. This setup also creates distinct service tiers, with audit trails showing exactly which features were accessed and by whom.
Advanced platforms take security further by using AES 256-bit rotating encryption with unique keys for each call. Even if there’s unauthorized access to the overall data pool, individual tenant information remains secure. Detailed analytics dashboards also track usage patterns and identify trends, providing actionable insights rather than superficial metrics. In fact, around 65% of users report that modern cloud systems make regulatory audits smoother.
"A solid audit trail can answer critical questions: Who accessed a recording? When did they do it? What did they do with it - listen, download, or delete? This creates a perfect, unbroken chain of custody, giving you undeniable proof of how data has been handled."
To further minimize risks, resellers should use automated retention management to delete expired records across all storage locations while keeping compliance-related logs for the required duration. Additionally, audit logs should capture pipeline-level events to ensure complete visibility.
Beyond data segregation, billing activities must also meet strict compliance standards.
Compliance with Stripe Rebilling Logs#
While tenant-specific logs handle data separation, maintaining detailed audit trails for billing systems is just as critical for SOC 2 compliance. Stripe audit logs play a key role by tracking sensitive activities like logins, changes to bank account details, API key generation, and administrative actions. These logs provide the transparency needed to trace actions around refunds, subscription updates, and payment processing.
Stripe itself is certified as a PCI Service Provider Level 1 and undergoes annual SOC 1 and SOC 2 Type II audits. When resellers use Stripe's automated rebilling, they benefit from this compliance framework while maintaining their own audit trails. Considering that 35.5% of global security breaches in 2024 were linked to third parties, the importance of vendor management and audit logging in payment systems cannot be overstated.
Resellers should enable Stripe's audit logs and integrate them with external SIEM (Security Information and Event Management) tools to monitor for suspicious activities in real time. Automated notifications for critical events - like logins from unknown IPs - reduce the burden of manual log reviews. Regularly pruning Stripe user access and API keys also ensures that only authorized personnel have access to sensitive billing data.
| Audit Log Category | Specific Events Tracked | SOC 2 Trust Service Criteria Supported |
|---|---|---|
| Administrative | API key generation, permission changes, webhook signatures | Security, Confidentiality |
| Financial | Refunds issued, subscription changes, bank account updates | Processing Integrity |
| Access | Logins, failed attempts, IP addresses, device IDs | Security, Privacy |
| System | Configuration changes, automated rebilling events | Availability, Processing Integrity |
Platforms like My AI Front Desk offer white-label programs with Stripe rebilling that can be set up in under 10 clicks. These systems handle backend processes while resellers focus on client relationships. Detailed analytics track every financial transaction and operational action, ensuring auditability for both SOC 2 and internal reviews.
21 CFR Part 11 Compliance in Pharmaceuticals#
Pharmaceutical companies, like many industries, depend heavily on audit trails. However, they face unique challenges tied to FDA regulations. For instance, operational calls - whether between sales teams and healthcare providers or internal discussions about adverse events - must include time-stamped audit trails to prove compliance with FDA-approved protocols. These records are critical for verifying adherence to product claims and proper adverse event reporting procedures.
Call recordings in this sector are more than just audio files - they're dynamic digital records that must preserve metadata and interactive elements to meet 21 CFR Part 11 standards. This means capturing not just the call itself, but also details like who accessed it, when, from where, and what actions were taken (e.g., listening, downloading, or deleting).
Modern audit systems offer immutable records, eliminating blind spots that manual sampling might miss. Automated systems ensure that every interaction is monitored, with over 95% precision in detecting violations. These systems also integrate with CRM platforms, linking call events to authorized user roles and logging any administrative changes, such as permission updates or user deletions. This creates end-to-end tracking, providing a complete historical view for FDA audits.
Time-Stamped Audit Trails for Operational Calls#
The cornerstone of 21 CFR Part 11 compliance is the time-stamped audit trail. Every action on a call recording - whether access, playback, or export - must be logged with sub-second UTC timestamps, user credentials, transaction details, and source identifiers like IP addresses or device IDs. This level of detail ensures an unbroken chain of custody, which auditors rely on.
For pharmaceutical companies, these trails serve two main purposes:
- They prove that product claims made during sales calls match FDA-approved indications.
- They demonstrate that adverse event reporting procedures were correctly followed.
For example, if a healthcare provider mentions a potential side effect during a call, the audit trail must confirm that the appropriate personnel were notified and the event was logged in the pharmacovigilance system within the required timeframe.
API workflows are vital for capturing this level of detail. These workflows track every event - from speech-to-text (STT) to large language model (LLM) inference and text-to-speech (TTS). This is especially critical when AI systems, such as virtual receptionists, handle patient inquiries or schedule appointments. Each interaction must be traceable to the system state and policies active at the time of the call.
| Audit Trail Component | Description | Compliance Value |
|---|---|---|
| User Credentials | Unique ID of the person performing the action | Ensures accountability and authority checks |
| UTC Timestamps | Precise time of event (often sub-second) | Establishes chronological order for compliance |
| Transaction Details | Specific action (e.g., access, play, delete) | Documents the chain of custody |
| Source Identification | IP address or device used for access | Confirms security and data origin |
| System State | Agent version and active policies at the time | Verifies regulatory compliance during the event |
To safeguard these audit trails, companies should use rotating encryption with AES 256-bit keys, ensuring each conversation is protected by a unique key. Automated retention management can further enforce deletion schedules while preserving records needed for active audits.
Standardized event classifications also play a key role. Using consistent labels like STT_RESULT or GUARDRAIL_TRIGGERED makes audit logs easier to query and interpret for regulators. Combined with detailed timestamps and strict access controls, this approach ensures that every interaction is properly documented and authorized.
Authority Checks and CRM Integration#
While time-stamped audit trails capture the "what" and "when", authority checks address the "who" and "why." The FDA requires pharmaceutical companies to prove that only authorized personnel accessed sensitive data and that every action is tied to a uniquely identifiable individual. Shared accounts fail compliance standards because they obscure accountability.
Identity and Access Management (IAM) platforms address this by logging every action, modification, or data access event with a specific "Actor" ID - whether it’s a User ID or API ID. These platforms enforce role-based access controls (RBAC), ensuring that sales reps can only access data relevant to their territories, while compliance officers have read-only access to audit logs.
"Audit trails provide a comprehensive record of user activities within a network or system, showing who did what and when. These logs play an important role in modern security, compliance, and fraud prevention." - Max Fathauer, Workforce IAM Evangelist, Ping Identity
CRM integration takes this further by linking call events with customer records and user permissions. For example, when a sales rep contacts a healthcare provider, the CRM logs the rep’s credentials, the provider’s account details, and any product information discussed. This creates a unified record that auditors can trace from the initial call through follow-up actions, such as sending samples or scheduling visits.
Platforms like My AI Front Desk simplify this process. Their API workflows automatically log CRM changes - like user deletions or permission updates - alongside call data. This ensures that audit trails remain intact even when personnel changes occur.
To maintain data integrity, companies should use WORM (Write Once Read Many) storage for audit logs and call recordings. This prevents unauthorized alterations to historical records, a critical requirement for FDA compliance. Audit logs should also be stored in immutable formats and retained for at least 366 days, often reaching petabyte-scale volumes.
Regular validation of logging systems is equally important. Companies must periodically review their CRM and call analytics tools to ensure all necessary data points are captured for 21 CFR Part 11 compliance. This includes verifying the accuracy of timestamps, the uniqueness of user IDs, and the completeness of transaction details.
Finally, personnel reviewing audit trails must have process-specific expertise. FDA regulations require that reviewers possess a deep understanding of the pharmaceutical processes involved, enabling them to identify unauthorized changes or deviations. For instance, compliance officers auditing call records should be well-versed in product promotion rules and adverse event reporting guidelines.
Multi-Channel Compliance in Retail#
Retailers today face unique challenges in managing customer interactions across multiple channels like calls, texts, emails, and chats - all while ensuring compliance with strict regulations. Imagine a customer texting about a product, calling to finalize the purchase, and later emailing with a question about their order. Without a unified audit trail, keeping track of these interactions for PCI DSS compliance becomes nearly impossible.
The stakes are high. Non-compliance can lead to massive fines under regulations like GDPR and PCI DSS. On average, non-compliance costs businesses $9.4 million, while maintaining compliance costs much less - around $3.5 million. The variety of communication methods only adds to the complexity.
Modern compliance platforms address this by consolidating all communication data into a "single pane of glass" - a unified system where every interaction is logged, searchable, and auditable. This ensures that no matter how a customer shares sensitive information, like a credit card number, the audit trail captures every detail: who handled it, when, what actions were taken, and whether sensitive data was properly handled.
Tracking Across Communication Channels#
To maintain a continuous audit trail, systems need to link interactions across all channels. For example, a web chat might lead to a follow-up phone call and then a text message confirmation - all tied to a single customer record.
My AI Front Desk excels in this area by using AI-generated metadata to document every interaction. Whether a customer calls, emails, or texts, the system automatically records key details like timestamps, call IDs, and actions taken (e.g., CRM updates or payment processing). This metadata forms the backbone of a searchable audit trail.
For text communications, the platform’s texting workflows and AI texting bot log every message exchange. For example, if a customer texts to check an order status, the system records the entire conversation and any related actions, like sending a follow-up email or updating the CRM. This creates a seamless chain of documentation that auditors can easily review.
Compliance also requires explicit consent before sending automated texts or making AI-driven calls. Violations can cost $500–$1,500 per call. AI agents can automatically request and log consent, embedding it into the metadata for every interaction, eliminating the need for manual processes.
In retail’s multi-channel environment, smart redaction plays a key role. This AI-driven feature automatically identifies and removes sensitive payment information from audio recordings and text transcripts. For example, sensitive audio is replaced with a flat tone, and sensitive text is masked.
"PCI DSS requires that payment card data never be stored in recordings unless encrypted with strict access controls."
- Andreea Tilibașa, Content Marketing Specialist, PBX.IM
Granular access controls add another layer of security. Role-based permissions ensure that only authorized personnel can view sensitive data. For instance, a store manager might review customer service calls without accessing payment logs, while compliance officers have read-only access to the audit trail.
These systems act like a digital black box, recording every action - who accessed a record, when, and whether it was downloaded or deleted. This ensures that even if someone tries to tamper with records, the audit trail preserves evidence of both the original issue and the tampering attempt.
Analytics Dashboards for Compliance Insight#
Traditional quality assurance (QA) methods typically review less than 2% of interactions, leaving significant blind spots. Just one unmonitored interaction where payment data is mishandled or a disclosure is missed can lead to a compliance violation.
Analytics dashboards solve this by auditing 100% of interactions across all channels. Instead of sampling a small fraction of communications, AI-powered systems review every call, text, and email, closing the gaps regulators often exploit. About 90% of call centers use recording software for quality control, and 65% report smoother audits due to better tracking.
These dashboards consolidate data from telephony systems, unified communication platforms, and text archives into a single interface. Compliance officers can search across all channels simultaneously, filtering by keywords, speaker, or intent. For example, searching for "credit card" instantly pulls up every interaction where payment information was discussed, making it easy to verify compliance protocols.
Real-time alerts transform compliance from reactive to proactive. If an agent forgets to give a required PCI DSS disclosure during a call, the system flags the issue immediately. Supervisors can intervene before the call ends, preventing violations from escalating. This "intelligent co-pilot" approach catches errors as they happen, rather than weeks later during manual reviews.
| Feature | Benefit for Retail Compliance |
|---|---|
| 100% Auditing | Eliminates blind spots and provides defensible evidence for regulators. |
| Real-Time Alerts | Enables immediate action on high-risk patterns or missed disclosures. |
| Automated Redaction | Protects sensitive data in audio and text. |
| Unified Dashboard | Ensures consistent compliance across all channels. |
| Immutable Audit Logs | Records every action, preventing tampering. |
Dashboards also provide sentiment and trend analysis, which adds context to compliance data. For example, they can track customer emotions across interactions, identifying patterns that might lead to disputes or compliance risks. A frustrated customer who escalates from a call to a text and then files a formal complaint creates a traceable pattern that compliance teams can address.
The My AI Front Desk analytics dashboard integrates searchable transcripts across all channels, allowing compliance officers to quickly retrieve records for audits or internal reviews. If an auditor requests documentation on how payment data was handled during a specific period, the dashboard can generate a detailed report within minutes.
Automated retention management ensures that data is stored only as long as necessary. Systems can automatically delete recordings, transcripts, and metadata once they reach their expiration date, based on legal or industry requirements. This minimizes liability by preventing data from being stored longer than needed.
"A well-defined retention policy is your best defense against two major risks: holding onto data for too long (which increases your liability) or deleting it too soon (which could violate regulations)."
- My AI Front Desk
Retailers can also translate complex compliance rules into machine-readable instructions within their dashboards. For example, a rule might state: "IF a customer provides a credit card number, THEN verify the agent delivered the required security disclosure". These rules allow the system to automatically flag violations, reducing reliance on manual interpretation.
The move from manual sampling to comprehensive AI monitoring doesn’t eliminate human oversight - it shifts its focus. QA auditors are evolving into "Compliance Strategists", concentrating on root causes and refining AI rules instead of monitoring individual calls. For instance, if recurring disclosure violations are flagged, these strategists investigate and implement solutions to prevent future issues.
These tools and processes highlight the critical role of audit trails in ensuring compliance across retail’s complex, multi-channel landscape.
Conclusion#
Audit trails are far more than a regulatory requirement - they are the backbone of vendor compliance across countless industries. From safeguarding patient health information in healthcare to securing financial transactions, managing multi-tenant SaaS platforms, ensuring pharmaceutical integrity, and tracking retail interactions, every action must be logged with accurate, unchangeable, and timestamped records.
The stakes are high: under GDPR, regulatory breaches can cost up to €20 million or 4% of annual global revenue, while HIPAA violations can result in penalties of $1.5 million annually per provision. On the flip side, 65% of users report smoother audits when using modern, cloud-based systems with comprehensive audit trails. By maintaining detailed, searchable records, organizations transform compliance from a frantic hunt for documentation into a seamless, proactive process. These robust systems not only reduce risks but also enhance operational efficiency.
"Regulators are no longer satisfied with organizations simply recording calls; they now expect organizations to govern them."
The advantages of strong audit trails are clear. Tools like My AI Front Desk offer precisely what businesses need: meticulously tracked, timestamped recordings that strengthen compliance strategies. Features like automated redaction ensure sensitive information is protected, while granular access controls restrict data interaction to authorized personnel. Integration with platforms like Zapier further centralizes compliance alerts and audit data, making it easier to stay ahead of regulatory requirements. This kind of unified approach highlights the critical role audit trails play across industries like healthcare, finance, SaaS, pharmaceuticals, and retail.
The numbers speak for themselves: the global conversation intelligence market, valued at $25.3 billion in 2025, is expected to grow to $55.7 billion by 2035. This growth reflects a broader understanding that compliance isn't just about avoiding penalties - it’s about earning trust. A well-maintained audit trail answers essential questions about who accessed data, what was done, when it happened, and why. For businesses managing vendor relationships, white-label services, or multi-channel interactions, this transparency turns compliance into a competitive edge.
FAQs#
What makes an audit trail 'tamper-proof' for call recordings?#
A "tamper-proof" audit trail ensures that metadata and conversation summaries are securely recorded in a way that prevents unauthorized changes or deletions. This is made possible through automated retention systems and detailed audit logs, which help maintain data integrity and ensure adherence to established policies.
How long should we retain call audit logs for different regulations?#
Retention periods for call audit logs vary depending on the regulations governing your industry. For instance, GDPR specifies a minimum of 30 days, whereas HIPAA requires retention for up to six years or longer. Additionally, certain industry-specific regulations may demand keeping records for several years, as directed by relevant authorities. It's crucial to verify the requirements specific to your industry and legal obligations.
What should an audit trail capture across calls, texts, and emails?#
An effective audit trail is all about capturing the right details. It should include call start and end times, participant information, and the type of communication used - whether it's a call, text, or email. For voice calls, it’s important to log consent records and securely store either conversation summaries or full transcripts. When it comes to texts and emails, the audit trail should document timestamps, content, and delivery status.
In industries with strict regulations, tracking who accessed the data and what changes were made is essential. This not only keeps things compliant but also promotes transparency.