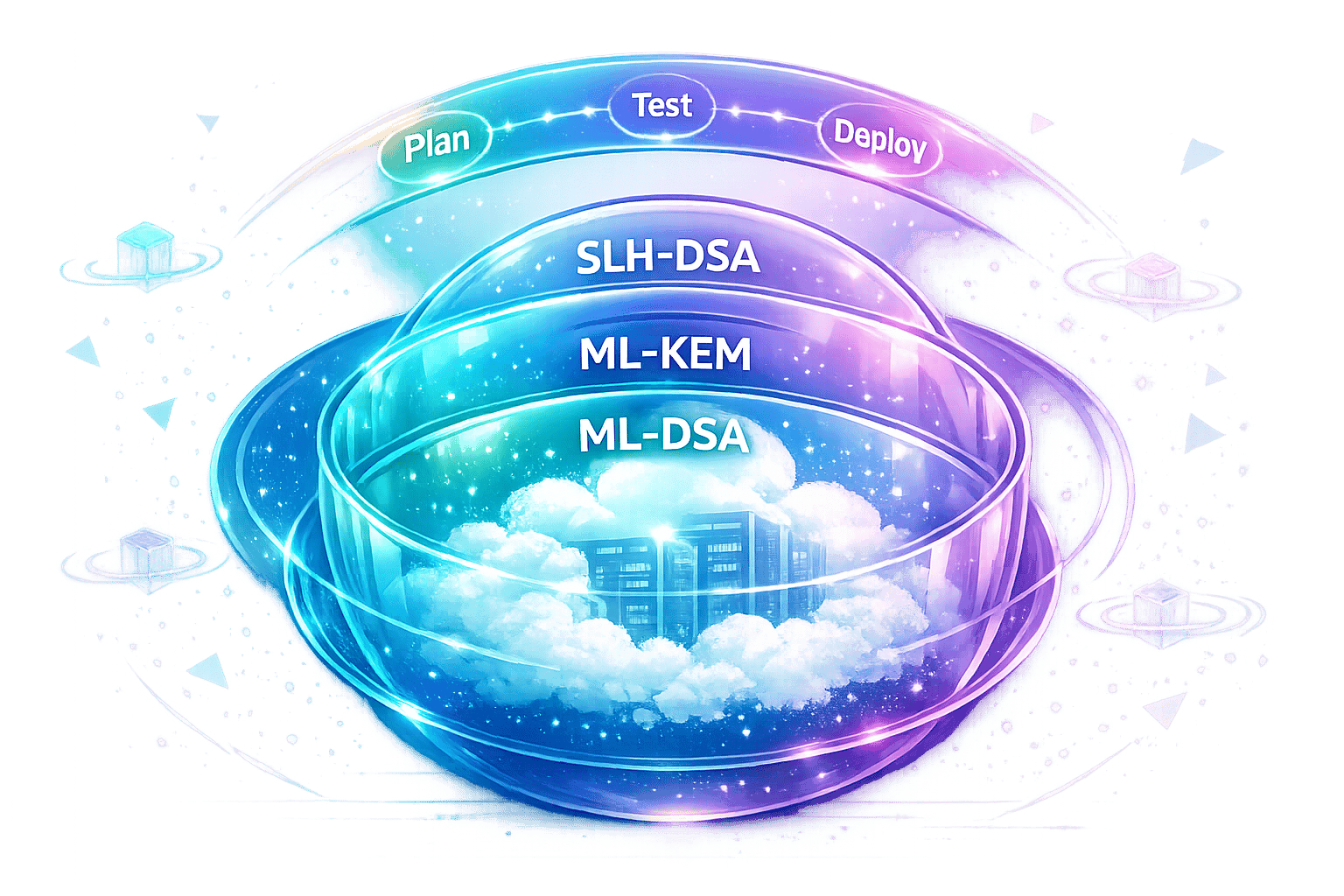
Quantum computers are set to disrupt current encryption, putting cloud security at risk. To counter this, NIST has finalized new post-quantum cryptography (PQC) standards designed to resist quantum attacks. These include FIPS 203 (ML-KEM) for secure key exchanges, FIPS 204 (ML-DSA) for digital signatures, and FIPS 205 (SLH-DSA) for long-term security. A fourth standard, FIPS 206 (FN-DSA), was added in 2025 for bandwidth-limited environments.
Key takeaways:
- Why it matters: Quantum computers could break RSA and ECC encryption, potentially exposing sensitive data.
- The threat: Old data is being collected now ("Harvest Now, Decrypt Later") for future decryption.
- The solution: Transition to quantum-resistant encryption like ML-KEM and hybrid models combining classical and post-quantum methods.
- Timeline: Federal systems must phase out vulnerable algorithms by 2035, with critical migrations starting now.
These standards are already being adopted by major cloud providers like Cloudflare and AWS, ensuring encrypted traffic and stored data remain secure against future threats. For businesses, the time to start upgrading is now.
NIST Post-Quantum Cryptography Update#
sbb-itb-e4bb65c
The NIST Post-Quantum Cryptography Standardization Process#
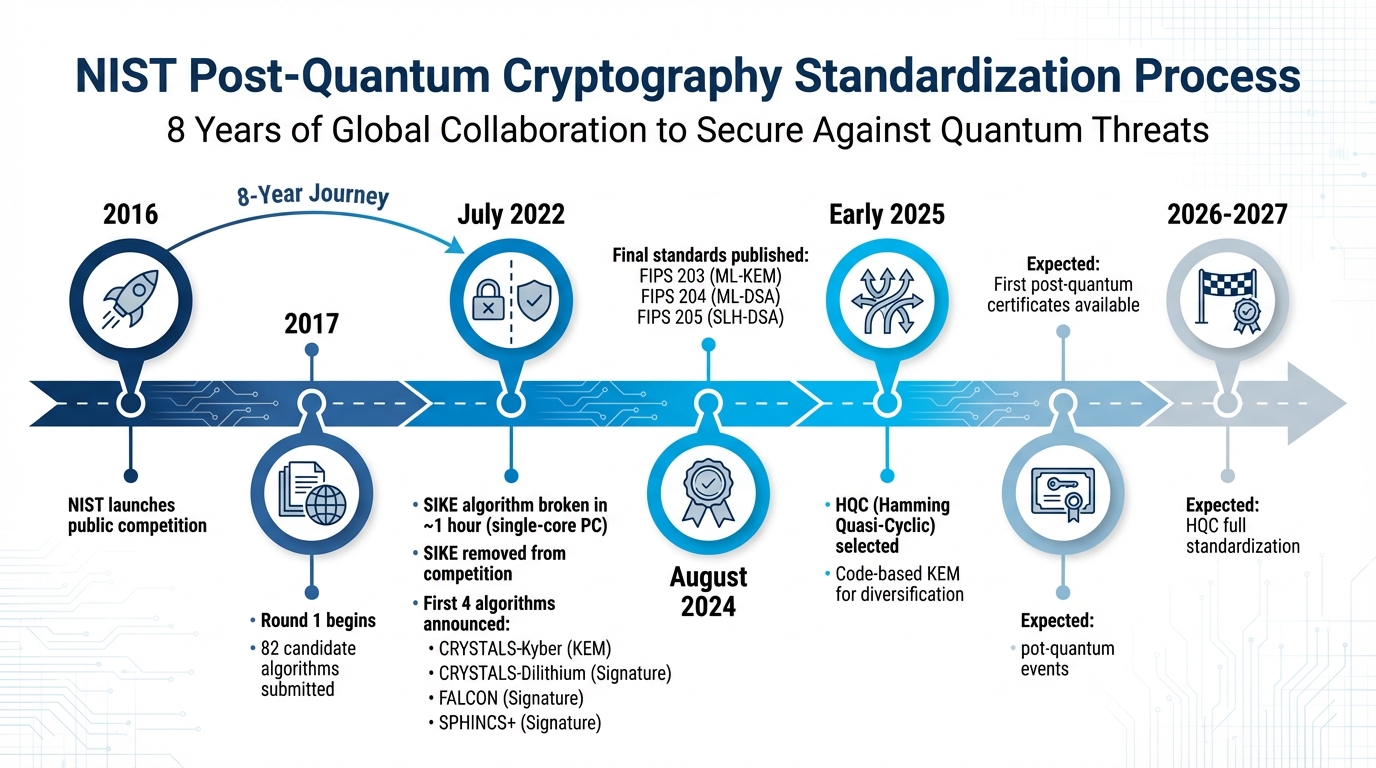
NIST Post-Quantum Cryptography Standardization Timeline 2016-2027
NIST kicked off its Post-Quantum Cryptography Standardization Project in 2016 with an open competition. Cryptographers from around the world were invited to submit algorithms designed to resist quantum attacks, aiming to eventually replace RSA and ECC encryption methods that are vulnerable to Shor's algorithm.
Timeline and Key Milestones#
The process officially began in 2017, when NIST received 82 candidate algorithms from international teams for the first evaluation round. Unlike traditional closed-door approaches, NIST encouraged open, global collaboration, inviting cryptographers to publicly examine and critique each submission.
This collaborative effort paid off. In July 2022, researchers Castryck and Decru demonstrated a critical vulnerability in the SIKE algorithm, breaking it in about one hour using a single-core PC. This led to SIKE's immediate removal from the competition. That same month, NIST announced the first four algorithms selected for standardization: CRYSTALS-Kyber (Key Encapsulation Mechanism), CRYSTALS-Dilithium (Signature), FALCON (Signature), and SPHINCS+ (Signature).
By August 2024, NIST finalized the first three standards - FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA) - marking the culmination of eight years of effort. In early 2025, NIST selected HQC (Hamming Quasi-Cyclic), a code-based KEM, to diversify beyond lattice-based algorithms. Full standardization of HQC is expected by 2026-2027.
| Year | Milestone |
|---|---|
| 2016 | NIST launches the public competition |
| 2017 | Round 1 begins with 82 candidate algorithms |
| 2022 | First four algorithms announced; SIKE removed after being broken |
| August 2024 | Final standards for ML-KEM, ML-DSA, and SLH-DSA published |
| Early 2025 | HQC selected for standardization |
| 2026 | Expected availability of first post-quantum certificates |
These milestones reflect NIST's thorough approach to selecting quantum-resistant cryptographic standards.
Goals and Objectives of the Initiative#
NIST's mission was clear: create cryptographic algorithms capable of resisting attacks from future quantum computers while maintaining practical performance for modern applications. A key concern was the potential for adversaries to collect encrypted data today, with plans to decrypt it once a cryptographically relevant quantum computer (CRQC) becomes available.
To address this, NIST focused on algorithm diversity. Instead of choosing a single "winner", the agency selected multiple algorithms based on different mathematical foundations, such as lattices, hashes, and codes. This diversity ensures alternative options are available if one mathematical assumption is compromised. Performance was another priority. NIST evaluated factors like key size, signature size, and computational speed to ensure the algorithms could function efficiently on the internet.
"This has been a monumental effort, and we would like to extend our gratitude to NIST and all the cryptographers and engineers across academia and industry that participated." - Luke Valenta, Vânia Gonçalves, and Bas Westerbaan, Cloudflare
The next section will explore the features of the approved cryptographic standards in detail.
Key NIST Post-Quantum Cryptographic Standards#
In August 2024, NIST finalized three key standards to address quantum computing threats, with a fourth expected in 2025. Each standard plays a unique role in securing cloud infrastructure against these emerging risks.
Overview of FIPS Standards#
FIPS 203 (ML-KEM), built on CRYSTALS-Kyber, is the backbone of cloud encryption. It handles key encapsulation, which establishes secure communication between servers and clients, replacing outdated RSA and Diffie-Hellman exchanges in protocols like TLS. For general cloud use, NIST recommends ML-KEM-768, which offers security comparable to 192-bit symmetric encryption. Performance-wise, ML-KEM-512 is a standout, managing tens of thousands of decapsulation operations per second, far surpassing RSA-2048’s limit of about 1,400 operations per second.
FIPS 204 (ML-DSA), derived from CRYSTALS-Dilithium, is the go-to standard for digital signatures in cloud authentication. It ensures identity verification and data integrity for TLS certificates, code signing, and API authentication. While ML-DSA signatures are 30–50 times larger than ECDSA signatures, their verification speed is approximately 20 times faster than ECDSA P-521.
FIPS 205 (SLH-DSA), based on SPHINCS+, serves as an alternative digital signature standard. It relies exclusively on hash functions like SHA-256, making it distinct from lattice-based algorithms. Although its signature sizes range from 7.8 KB to over 40 KB, which limits its suitability for high-traffic scenarios, it excels in long-term applications such as root certificate authorities.
FIPS 206 (FN-DSA), built on FALCON, is optimized for bandwidth-restricted environments. Its signatures, as small as 666 bytes, make it ideal for applications like DNSSEC and IoT devices where data size is a critical factor. However, its reliance on floating-point arithmetic and FFT-based operations complicates its implementation.
The table below provides a quick comparison of these standards, highlighting their strengths and intended cloud applications.
Algorithm Comparison Table#
| Standard | Primary Use | Mathematical Basis | Key Feature | Cloud Application |
|---|---|---|---|---|
| FIPS 203 (ML-KEM) | Key Encapsulation | Module-Lattice | Fast operations | TLS key exchange, VPN tunnels |
| FIPS 204 (ML-DSA) | Digital Signatures | Module-Lattice | Fast verification | WebPKI certificates, code signing |
| FIPS 205 (SLH-DSA) | Digital Signatures (Backup) | Stateless Hash | High security, large size | Root CAs, long-term archives |
| FIPS 206 (FN-DSA) | Digital Signatures (Compact) | NTRU-Lattice | Smallest signatures | DNSSEC, IoT, constrained networks |
Major cloud providers like Cloudflare, Google, and Amazon are already adopting hybrid modes that combine classical algorithms (e.g., X25519) with post-quantum standards (e.g., ML-KEM) to protect against both current and future threats. For example, in February 2026, Cloudflare upgraded its Cloudflare One SASE platform to include hybrid ML-KEM in its IPsec product, extending quantum-resistant encryption to corporate networks.
How Post-Quantum Standards Affect Cloud Security#
The adoption of NIST's post-quantum standards marks a major shift in how cloud systems defend against the looming threat of quantum computing. Encryption methods like RSA and Diffie-Hellman, which currently secure most cloud communications, are at risk due to Shor's algorithm - a quantum computing breakthrough capable of breaking a 2048-bit RSA private key in mere hours. This creates two major vulnerabilities that NIST's new standards aim to address: securing key exchanges and safeguarding long-term data privacy.
Quantum-Resistant Key Establishment#
ML-KEM (FIPS 203) is designed to replace outdated and vulnerable classical key exchanges used in protocols like TLS and VPNs. Unlike traditional methods that rely on integer factoring or discrete logarithms, ML-KEM leverages the Learning With Errors (LWE) problem over module lattices, which is resistant to quantum attacks. Not only does ML-KEM provide this advanced security, but it also offers faster decapsulation compared to RSA-2048. This efficiency means cloud providers can adopt quantum-resistant encryption without significantly impacting system performance.
Some cloud providers have already embraced hybrid key exchange models that combine classical and post-quantum algorithms. This dual approach ensures security even if one of the algorithms is compromised in the future. By February 2026, Cloudflare enhanced its Cloudflare One SASE platform to fully support post-quantum encryption. Researchers Sharon Goldberg and Amos Paul integrated hybrid ML-KEM into the IPsec product, securing critical corporate network connections.
Addressing 'Harvest-Now, Decrypt-Later' Threats#
Post-quantum standards also tackle the critical issue of stored data vulnerability. One of the most pressing concerns is the "harvest-now, decrypt-later" (HNDL) attack model. In this scenario, attackers are already collecting encrypted cloud traffic with plans to decrypt it once quantum computers become powerful enough. Cloudflare researchers explain:
"In what is known as the 'harvest now, decrypt later' threat model, an adversary can store encrypted data until some point in the future when they gain access to a sufficiently large quantum computer, and then can decrypt at their leisure".
This makes upgrading key agreement protocols an urgent priority, as they protect the long-term privacy of stored data. While digital signatures are critical for preventing real-time impersonation attacks, key agreement protocols safeguard sensitive data with long shelf lives - such as government records, financial data, and medical information. These data types, often needing protection for 10 years or more, must transition to quantum-resistant standards immediately. Fortunately, post-quantum key exchanges only add about 1–2 milliseconds of latency to TLS handshakes under optimal conditions, making the upgrade feasible for most cloud applications without noticeable performance trade-offs.
NIST Transition Timelines and Recommendations#
Federal mandates, building on NIST's post-quantum standards, now outline clear steps to safeguard national systems against future quantum threats.
Federal Transition Requirements#
Under the Federal CNSA 2.0 guidelines, U.S. national security systems must fully transition to post-quantum cryptography by 2035. Prior to this deadline, systems are required to phase out 112-bit mechanisms, such as RSA-2048, by 2031. Meanwhile, Canada has set its own timeline, requiring organizations to submit a post-quantum migration plan by April 2026 and complete critical system migrations by the end of 2031. These milestones ensure a phased, structured approach to upgrading security across national systems.
Crypto-Agility and Immediate Steps#
NIST has emphasized the immediate integration of cryptographic tools like ML-KEM, ML-DSA, and SLH-DSA into products and protocols. This highlights the importance of crypto-agility - designing systems that can adapt to new cryptographic algorithms without requiring extensive infrastructure changes. For instance, cloud providers are encouraged to adopt hybrid models that combine classical algorithms, such as X25519, with post-quantum options like ML-KEM. This approach helps address both current threats and potential vulnerabilities in emerging standards. Some major tech companies have already started deploying hybrid key agreements to stay ahead of the curve.
Organizations are also advised to inventory their cryptographic applications to identify and prioritize systems protecting long-term sensitive data, such as personal information, intellectual property, and government records. Additionally, cloud providers should prepare for increased demands on network and storage resources, a key factor in federal system transition planning.
The table below outlines the transition timeline, comparing current practices with the upcoming federal mandates.
Transition Timeline Comparison Table#
| Period | Symmetric Key Requirements | Asymmetric Algorithm Requirements | System Focus |
|---|---|---|---|
| Pre-2030 | AES-128/256; SHA-256 | RSA-2048+; ECC (P-256); Hybrid PQ testing | Preparation & Hybrid Deployment |
| 2030-2035 | AES-256 recommended; SHA-384 | Transition to ML-KEM (FIPS 203) & ML-DSA (FIPS 204) | Federal Compliance (NSM 10) |
| Post-2035 | AES-256; SHA-384+ | Full Post-Quantum (ML-KEM, ML-DSA, SLH-DSA, FN-DSA) | Mandatory Quantum-Resistance |
Additional Algorithms and Future Developments#
NIST is not stopping with its initial post-quantum cryptography standards. To ensure long-term security and stay ahead of potential vulnerabilities, the organization is working on backup algorithms and exploring new cryptographic methods. This proactive approach includes diversifying mathematical foundations to safeguard against potential weaknesses in current standards like ML-KEM or ML-DSA.
Backup Algorithms and Future Standards#
In March 2025, NIST selected HQC (Hamming Quasi-Cyclic) as a primary backup algorithm, with plans to finalize it by 2027. Unlike the lattice-based structure of ML-KEM, HQC uses error-correcting codes, offering a different mathematical foundation. Dustin Moody, who leads NIST's Post-Quantum Cryptography project, underlined the importance of having a backup standard to address any vulnerabilities that might arise.
For digital signatures, NIST is also advancing options like FN-DSA (Falcon) for quantum-resistant security. In October 2024, the organization selected 14 candidate signature schemes from an initial pool of 40 submissions to serve as potential future backups. These candidates include a range of approaches:
- Code-based schemes like CROSS and LESS
- Isogeny-based methods such as SQIsign
- Multivariate quadratic algorithms like MAYO
The need for this variety became evident after researchers Wouter Castryck and Thomas Decru successfully broke the SIKE algorithm in just about an hour using a single-core PC. This discovery led NIST to remove SIKE from consideration immediately, reinforcing the importance of mathematical diversity in post-quantum cryptography.
Workshops and Community Collaboration#
NIST also emphasizes community involvement to refine and expand its cryptographic standards. Through workshops and collaborative initiatives, researchers and industry leaders contribute to the development of new solutions. For example, the MPTS 2026 workshop (held January 26–29, 2026) focused on creating multi-party threshold schemes, which distribute keys to eliminate single points of failure.
Real-world applications are already shaping these efforts. Major cloud providers like AWS and Cloudflare are implementing post-quantum solutions and sharing their experiences. In February 2025, AWS integrated ML-KEM into its open-source AWS-LC library. Meanwhile, by mid-August 2024, Cloudflare's hybrid deployment of ML-KEM with X25519 was already safeguarding over 16% of human-generated traffic to its servers. These practical deployments not only validate the security of post-quantum algorithms but also help streamline their adoption across industries.
Conclusion#
NIST's newly established standards represent a major step forward in protecting cloud infrastructure from quantum-era threats. Quantum computing isn't some far-off concept - it's a present and pressing issue that requires immediate attention. The finalized post-quantum cryptography standards (FIPS 203, 204, and 205) lay the groundwork for defending against both today's "harvest now, decrypt later" tactics and tomorrow's quantum-powered decryption capabilities. As Dustin Moody, head of NIST's PQC Standardization Project, put it:
"We encourage system administrators to start integrating them into their systems immediately, because full integration will take time".
The effectiveness of these standards is already being proven in the field. Major industry leaders are integrating post-quantum protocols, demonstrating that this isn't just theoretical - it’s happening now.
For small businesses and cloud providers, the next steps are straightforward. Start by pinpointing where your current systems rely on quantum-vulnerable encryption methods like RSA or ECC. Transition to ML-KEM (FIPS 203) for key exchanges and discuss post-quantum strategies with your vendors. Hybrid approaches that combine classical and post-quantum algorithms can offer an extra layer of security during this transition. Auditing systems and collaborating with vendors ensures a smoother path to post-quantum readiness.
The clock is ticking. NIST aims to phase out quantum-vulnerable algorithms by 2035, but high-risk systems should act much sooner. Historically, integrating new cryptographic algorithms into global systems has taken 10 to 20 years. With the standards finalized, tools in hand, and the threat looming, the time to act is now.
FAQs#
Do I need post-quantum encryption now?#
Yes, it’s time to start planning for post-quantum encryption. The National Institute of Standards and Technology (NIST) has finalized its initial standards to address the risks posed by quantum computers. Many organizations are targeting a transition to these standards by the early-to-mid 2030s. Taking steps now will help ensure your systems stay secure as quantum computing continues to evolve.
What is hybrid PQC in TLS and VPNs?#
Hybrid Post-Quantum Cryptography (PQC) in TLS and VPNs merges classical cryptographic methods with quantum-resistant algorithms to protect against potential quantum computing threats. By combining traditional techniques like RSA or ECC with post-quantum solutions, such as lattice-based algorithms, this approach ensures secure communication during the shift to quantum-safe encryption. The dual-layered setup offers an extra layer of protection - if one encryption method is compromised, the other can still maintain security, making the transition to quantum-resistant standards more reliable.
Which systems should migrate first?#
Systems relying on RSA or elliptic curve cryptography (ECC) are particularly at risk from quantum attacks. These encryption methods could be easily compromised by quantum computers, making them a high priority for migration to post-quantum cryptography (PQC) standards.
Special attention should go to critical systems handling sensitive data, such as those in financial services or healthcare. These sectors often deal with highly confidential information, making them prime targets for potential breaches.
By planning ahead and updating cryptographic protocols proactively, organizations can reduce future risks and stay aligned with emerging NIST standards. Early action ensures better protection and smoother transitions in the face of evolving threats.